Every business runs on access – access to buildings, vehicles, equipment, and sensitive spaces. Yet behind this daily flow lies one of the most overlooked operational risks: unmanaged physical keys. From misplaced master keys to untracked asset access, even small gaps can quickly turn into costly security and efficiency problems. As organizations scale, relying on manual logs or outdated systems no longer holds up. This is where modern key management systems step in , transforming how businesses control, track, and secure their keys and assets with real-time visibility, accountability, and automation built into every interaction.

What Are Key Management Systems?
Every business , from a 10-unit apartment building to a 500-vehicle automotive fleet — runs on access. Access to rooms, equipment, vehicles, storage, and sensitive areas. And at the center of all of it, more often than not, are physical keys.
Key management systems (KMS) are structured solutions , combining secure hardware, intelligent software, and defined protocols — that control who has access to physical keys, when they can access them, and what happens when those keys move. A proper key control system replaces guesswork with accountability, and paper logs with real-time digital records.
Unlike a hook on a wall or a sign-out sheet on a clipboard, key management systems provide a full audit trail of every key interaction. They set access permissions by role, generate usage reports, send alerts for overdue returns, and integrate with broader security infrastructure. The result isn’t just tidier key storage — it’s a fundamentally different level of operational visibility.
| You Can Also Read : How Smart Lockers Are Redefining Secure Storage |
“When you can’t answer the question ‘who has the key right now,’ you’ve already lost control of your facility.”
Modern key management systems range from mechanical peg boards to digitally controlled smart cabinets with biometric authentication. The right system depends on your scale, industry, and security needs — but the principle is universal: every key should be traceable, every access accountable.
Why Businesses Need Key Control and Asset Tracking

The problem usually begins before anyone notices it. A maintenance team member borrows a master key for a quick job. A contractor signs out a vehicle key and leaves the site. A property manager lends a unit key and forgets to log it. None of these feel like security incidents in the moment , but each one creates a gap.
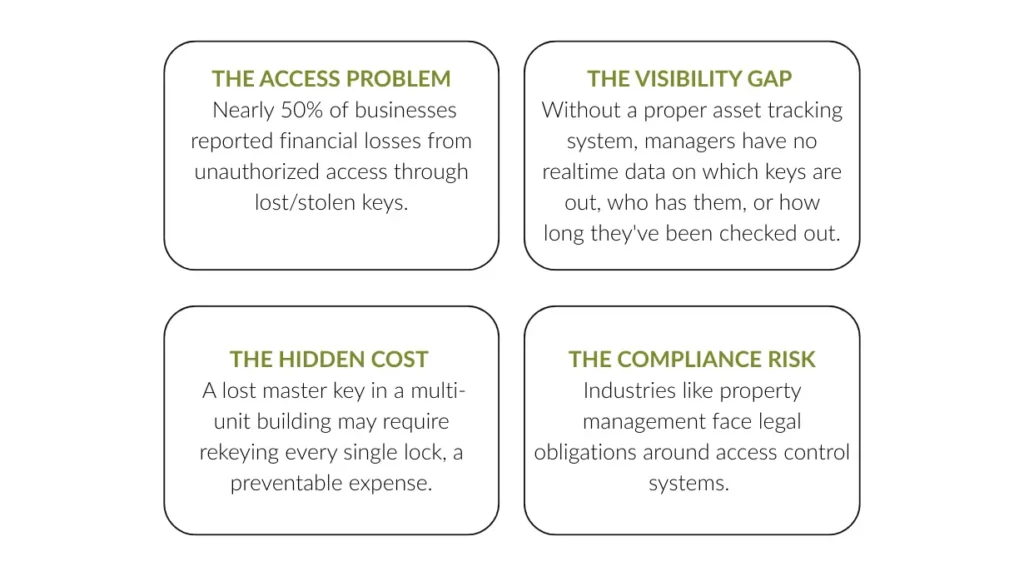
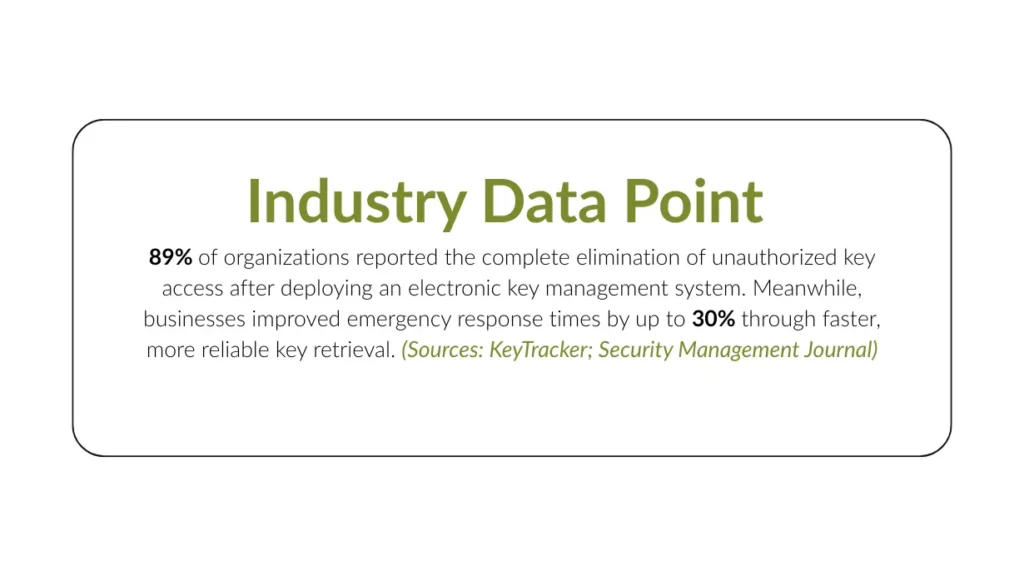
A robust key control system directly addresses these gaps. And when it’s paired with an asset tracking system, businesses gain something even more powerful: a complete picture of where every key, piece of equipment, and critical asset is at any moment. The operational case is clear , and so is the financial one. Organizations using structured access control systems can reduce unauthorized access incidents by up to 80%, according to the Security Industry Association.
How Key Management Systems Work in Business Operations

A well-designed key management system doesn’t operate in isolation — it fits into the rhythm of your daily operations. Here’s how the components work together:
- Secure Key Storage
Keys are stored in a locked, tamper-evident cabinet or smart locker, with each key assigned a designated slot. A secure key storage system ensures that no key can be removed without triggering a logged event, even if the cabinet door is left open. - Identity-Based Access Control
Users must authenticate via PIN, RFID badge, or biometric scan before any key is released. This enforces centralized key management, where permissions are assigned by role or individual. Unauthorized users cannot retrieve keys, regardless of their physical proximity to the cabinet. - Real-Time Key Tracking
Every key checkout and return is automatically time-stamped and logged. The system creates a complete audit trail that records who accessed a key, when it was taken, and how long it was in use. This information is accessible from any device. - Alerts and Automated Notifications
If a key is not returned on time or an access attempt occurs outside permitted hours, the system sends automatic alerts to the relevant manager. This eliminates the need for manual monitoring. - Reporting and Analytics
Management dashboards provide insights into key usage patterns, peak access times, frequently used assets, and potential anomalies. This transforms key data into actionable operational intelligence.
| You Can Also Read : Why Businesses Need Smarter Key Management |
Managing Keys and Assets with Software and Automation
Hardware handles storage. Software handles intelligence. Key management software is the layer that transforms a secure cabinet into a dynamic operational tool — giving managers the ability to track keys and assets across departments, locations, and shifts from a single dashboard.
Modern platforms allow administrators to set granular access rules: a technician may access vehicle keys only during working hours; a property manager may check out unit keys but not master keys; a contractor receives temporary access for a defined period only. When someone leaves the organization, their access is revoked instantly — no lock changes required.

For businesses operating across multiple sites, key management software enables centralized oversight with localized control. Site level managers see their assets; regional managers see everything. Reports can be scheduled, exported, and shared with compliance teams or auditors.
This is where solutions like Noki Exec come in. Noki Exec brings together secure key storage hardware with purpose-built software designed for the multi-residential, automotive, and construction environments where key and asset management complexity is highest.
Industries That Rely on Key Management Systems
Key management is not a niche requirement. It is essential infrastructure across industries where secure access, accountability, and operational efficiency are critical. Noki’s smart key management systems support a wide range of sectors:
| Industry | Key Challenges | How KMS Helps |
|---|---|---|
| Construction | Constant movement of contractors, multiple sites, risk of lost or misused keys | Tracks who has which key across sites and shifts, reducing theft and liability |
| Property Management | Managing unit keys, master keys, and tenant access | Ensures controlled access, maintains audit logs, supports compliance requirements |
| Logistics & Fleet | Vehicle key tracking, driver accountability, shift-based usage | Links keys to drivers and usage time, improving visibility and operational efficiency |
| Automotive | Handling large volumes of vehicle keys daily | Reduces time spent searching keys, improves staff productivity, prevents losses |
Smart key management systems bring structure, visibility, and control to industries where managing physical access is critical to daily operations. Across all these industries, the challenge is fundamentally the same: managing physical access at scale without losing control. Whether it’s keys to a vehicle, a unit, or critical equipment, businesses need a system that replaces manual guesswork with real-time visibility, accountability, and efficiency — making key management not just a security function, but a core operational advantage.
Improving Accountability and Access Control Across Teams
Access control systems traditionally focus on who gets through the door. But true accountability goes deeper — it covers what happens after the door opens. Who used the key? What did they access? Was it within their authorized scope?
Centralized key management enables a standard of accountability that manual systems simply cannot match. Every action is logged. Every anomaly is visible. And because users know they’re being tracked, behavior shifts — studies show that auditable systems alone reduce policy violations, not just detect them.
For multi-team environments, key management software platforms allow role-based access hierarchies: different departments have access to different key sets, with escalation protocols for exceptions. Audit reports can be generated on demand , useful for internal reviews, insurance claims, and regulatory compliance. The access control systems that matter most aren’t just the ones on the front door. They’re the ones governing everything behind it.
Choosing the Right Key Management System for Your Business
The right key management system is the one your team will actually use — and that fits the physical and operational reality of your environment. Here are the core considerations:
| Factor | What to Consider | Why It Matters |
|---|---|---|
| Scale & Capacity | How many keys and assets do you manage across locations? | A small office may need a 20-key setup, while construction or logistics operations require high-capacity systems with multi-site control. |
| Authentication Level | What level of access control is required? (PIN, RFID, biometric) | Higher-security environments benefit from advanced authentication, ensuring only authorized personnel can access critical assets. |
| Software Integration | Does it connect with your existing systems (HR, fleet, property management)? | Integration removes manual work, reduces errors, and keeps access data synchronized across platforms. |
| Remote Visibility | Can you monitor and manage keys in real time from anywhere? | Cloud-based dashboards provide full visibility, instant alerts, and reporting — even across multiple locations. |
Ultimately, the best system is the one that removes friction from daily operations while adding accountability across all access points. Start by auditing your current key workflow — identify the gaps, the risk points, and the moments where visibility is lost. That’s where your system needs to begin.
Ready to see what structured access control looks like for your specific environment?
Get in touch with the Noki team or book a demo — we’ll walk through your use case and show you exactly how Noki can close the gaps.
FREQUENTLY ASKED QUESTIONS
Q: What is the difference between a key management system and an access control system?
A:
An access control system manages entry to physical spaces such as doors, gates, and elevators. A smart key management system, on the other hand, controls the physical keys themselves.
Q: How does key management software support compliance?
A:
Smart key management systems automatically generate timestamped audit logs for every key transaction. For regulated industries like property management, healthcare, and automotive, these logs act as documented proof of controlled access.
Q: Can a key management system work across multiple locations?
A:
Yes. Modern smart key management systems are built for multi-site operations. They allow corporate or regional managers to monitor and manage all locations from a centralized dashboard, while still giving on-site teams appropriate local access and control.
Q: How quickly can a business see ROI?
A:
Most businesses start seeing measurable results within the first 90 days, including:
- Reduced key loss incidents
- Faster key retrieval (from 15+ minutes to under 3 minutes)
- Lower rekeying costs
- Reduced administrative workload
In some industries, like automotive, businesses report recovering thousands annually in productive time alone.
Q: Is physical key management still relevant with smart access technology?
A:
Absolutely. Physical keys remain one of the most cost-effective and reliable access methods — especially for vehicles, equipment, and legacy infrastructure.




